- Advertising
- Bare Metal
- Bare Metal Cloud
- Benchmarks
- Big Data Benchmarks
- Big Data Experts Interviews
- Big Data Technologies
- Big Data Use Cases
- Big Data Week
- Cloud
- Data Lake as a Service
- Databases
- Dedicated Servers
- Disaster Recovery
- Features
- Fun
- GoTech World
- Hadoop
- Healthcare
- Industry Standards
- Insurance
- Linux
- News
- NoSQL
- Online Retail
- People of Bigstep
- Performance for Big Data Apps
- Press
- Press Corner
- Security
- Tech Trends
- Tutorial
- What is Big Data
Keep Your Pet's Name to Yourself: WHM Password Security 101
Web services today are constantly targeted by brute force attacks that try to guess a user’s password to hack the account or steal information. Using a simple password like your pet's name will not work anymore. Enforcing a policy of strong passwords is a vital element of server security. WHM already includes the tools needed for securing passwords, so let’s see how you can configure them for optimal results.

Password Strength Configuration
WHM allows the administrator to set-up a general required password strength that is applied server-wide. You can find the Password Strength Configuration interface in the Security Center section of the menu.
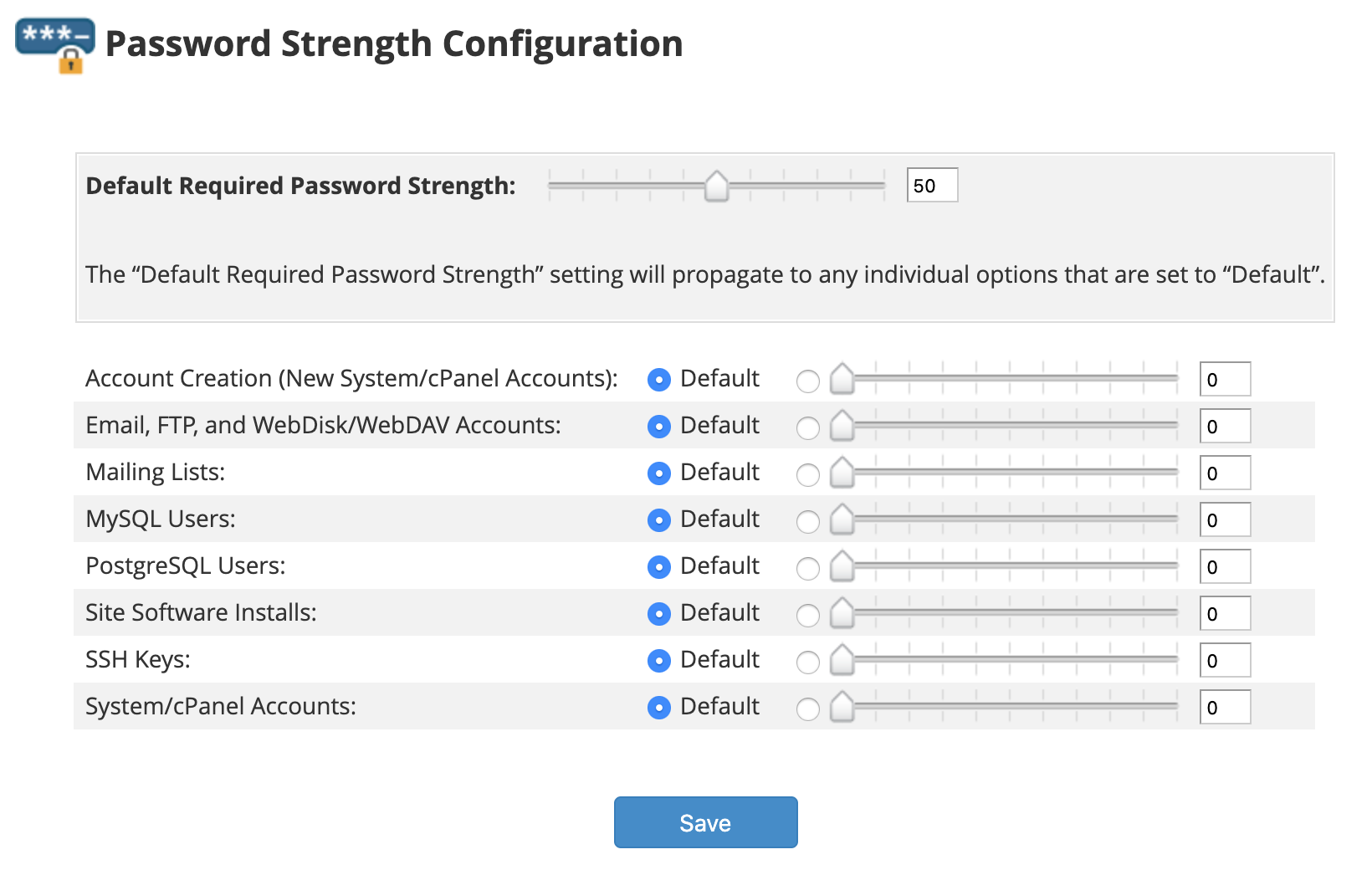
The default required password strength propagates to all default services and is scaled between 0 and 100, with 100 being the highest strength. It starts with the value of 50 and can be adjusted as needed. While cPanel recommends a strength of at least 40, the optimal value is 60 or more. You can also configure individual values for each service, depending on your needs and preferences; for instance, you can set a higher value only for email accounts.
Keep in mind these two caveats:
- These policies only apply to new accounts. If you want to enforce them to accounts that already exist, you can do so from the Configure Security Policies menu, which is described in the next section.
- The requirements are not applied if a user with shell access changes his password using the Linux passwd command.
Security Policies
Located in the Security section of the main WHM menu, the Configure Security Policies interface provides several additional options that apply to WHM, cPanel and webmail.
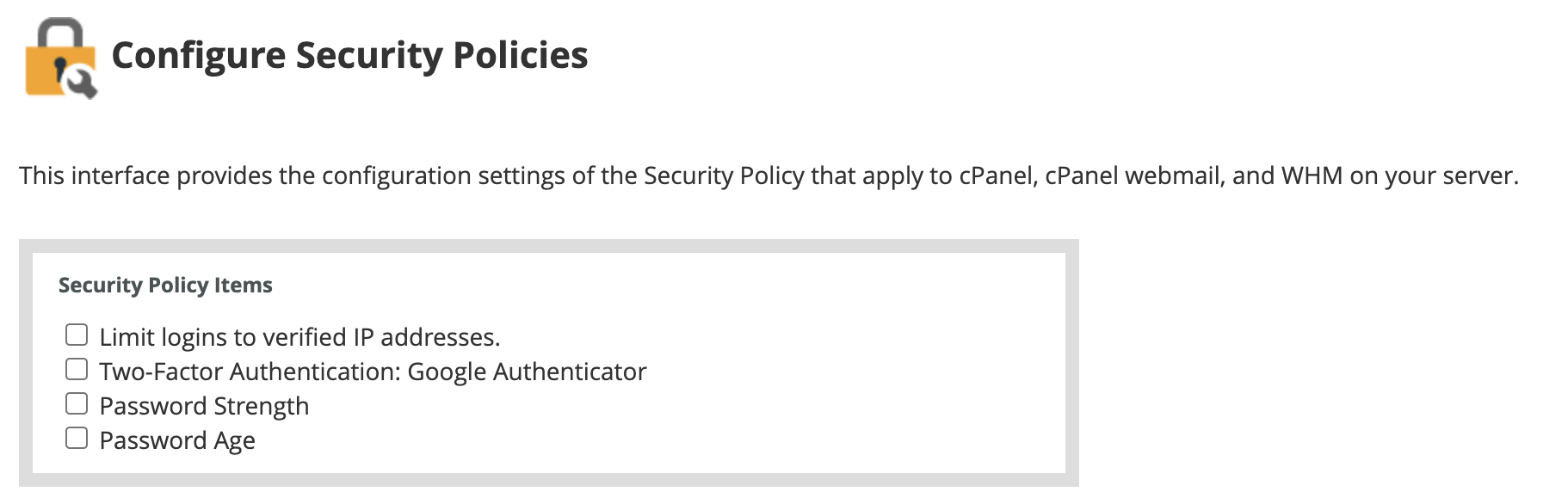
Let’s see what each option means.
1. Limit logins to verified IP addresses
The first option might sound a bit confusing. Activating it requires users to answer security questions when logging in from unknown IPs.
However, to set the security questions and add/remove the verified IP addresses you need to navigate to a different WHM interface: Home – Security Center – Security Options.
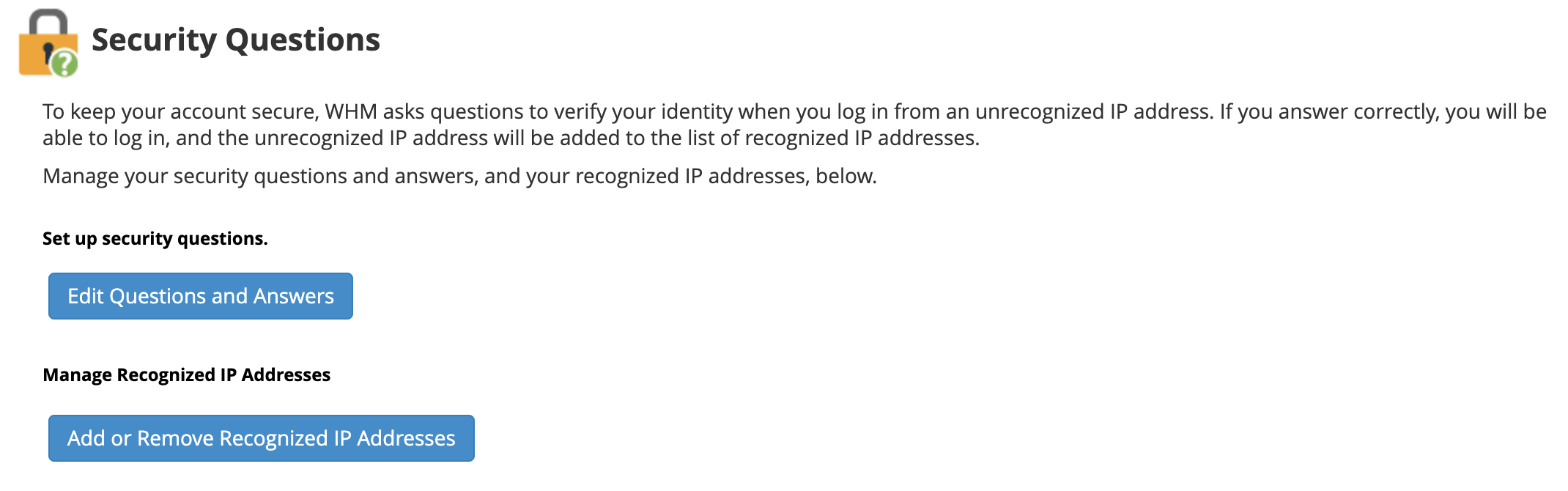
The initial IP address used when setting up the security questions is automatically added to the list of verified IPs. The list can be managed any time by clicking on the Add or Remove Recognized IP Addresses button.
When connecting from an unverified IP, users will be prompted to answer the security questions. If successful, the IP is added to the recognized list.
2. Two-Factor Authentication
This next setting can enable 2FA, requiring users to enter an additional code generated by a smartphone app when logging in.
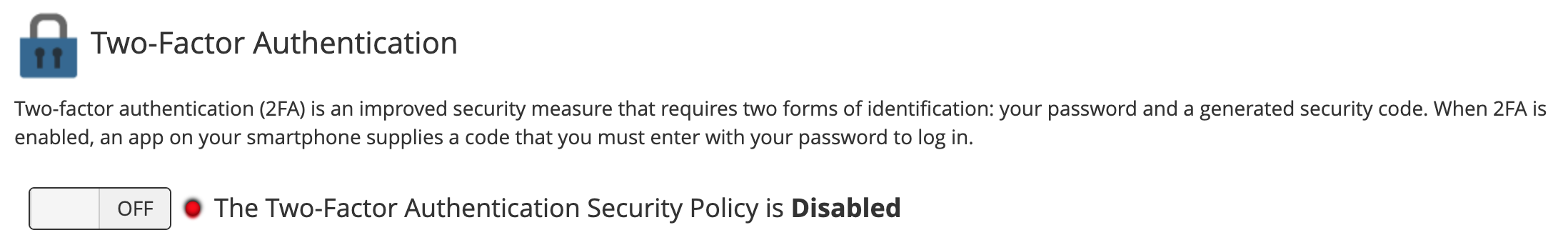
The settings are configured from a separate Two-Factor Authentication interface. Even if the security policy only mentions Google Authenticator, several other similar smartphone apps, such as Duo Mobile, are also supported.
3. Password Strength
Activating the third option will enforce strength requirements on all accounts, including existing ones.
4. Password Age
This last security policy can be activated to force users to reset a password after a configured number of days.
Other Security Tweaks
If you only connect to WHM services from several IP addresses or ranges, you can deny access from all other IPs to increase server security.
To configure this, navigate to the Host Access Control interface in the Security Center menu.
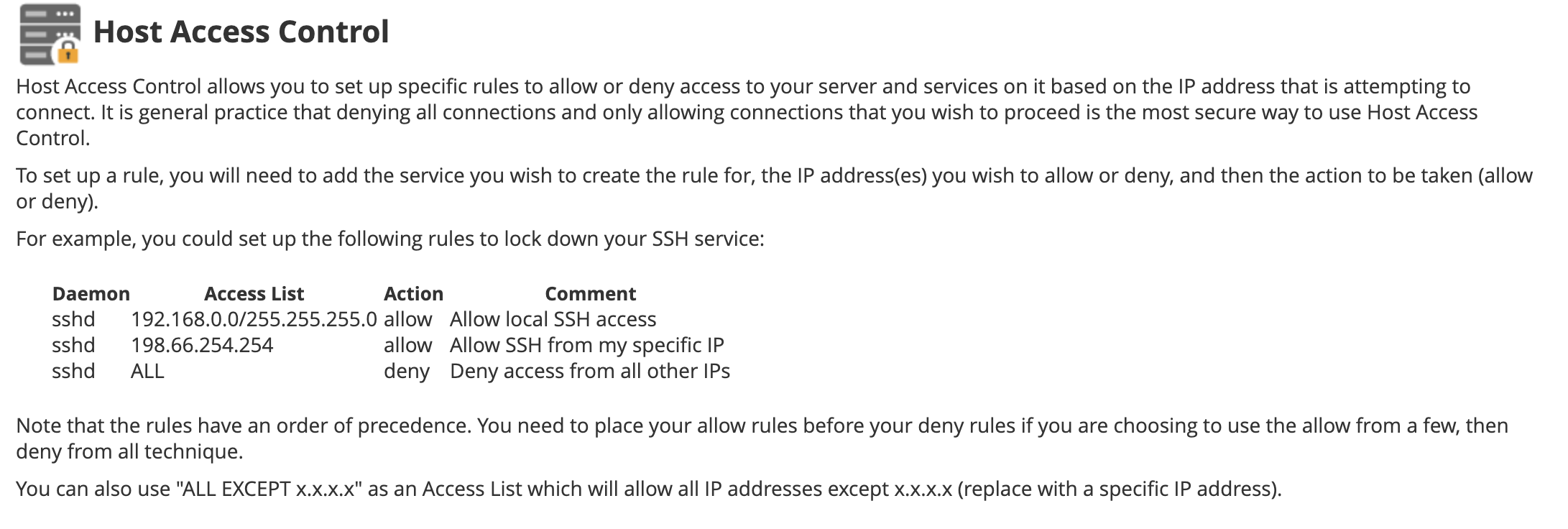
We won’t go into details regarding this interface now, since it is outside of the scope of this article, but it is a powerful and flexible feature that can be customized for specific services, such as FTP, SMTP, POP3 or IMAP.
Finally, the Home – Server Configuration – Tweak Settings interface includes additional password-related settings.

You can for example allow domain owners to use their password to access any email account of the domain or to prevent browser password caching for WHM, cPanel or webmail logins.
While no server can ever be 100% secure if outside connections are allowed, implementing the password policies detailed in this article will significantly reduce the risk of intrusion or hacks. For any other questions regarding best server security practices, you can always ask one of our sysadmins.
Readers also enjoyed:

How to Configure the Best TLS Settings in WHM: From A to A+


Leave a Reply
Your email address will not be published.